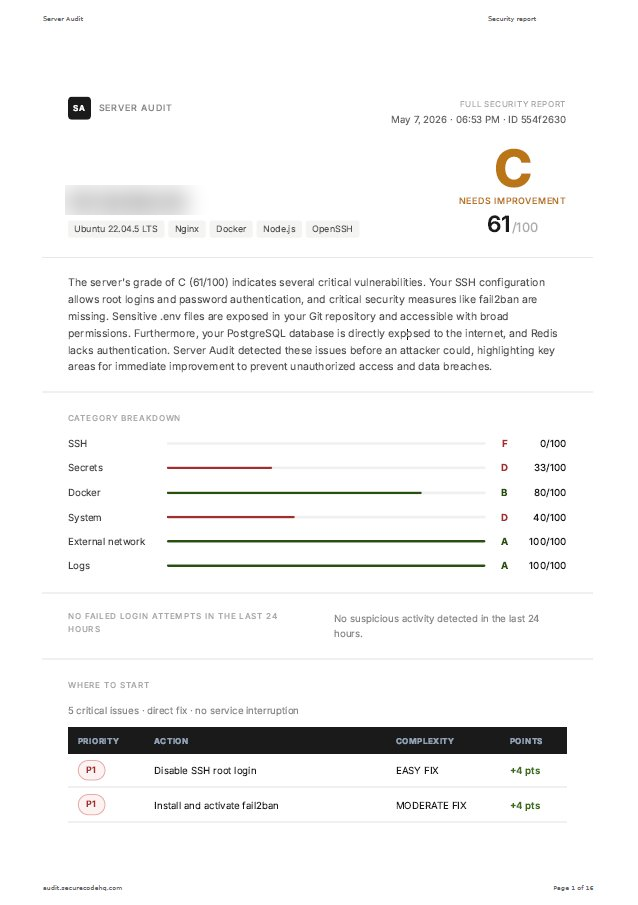
SSH root login enabled Direct root access enabled. Any attacker who guesses the password gains full control of the server. | Free | Critical |
SSH on default port Port 22 is the first one automated bots scan. Changing it reduces attack noise. | Free | Warning |
Password login enabled Passwords can be brute-forced. SSH key-only login prevents this entirely | Paid | Warning |
Unknown SSH keys Unexpected keys in authorized_keys could mean someone has access you didn't authorize | Paid | Info |
Credentials exposed in Git Database passwords and API keys committed to a repository, visible to anyone with repo access | Free | Critical |
Pending security patches Known vulnerabilities with public exploits that haven't been patched yet | Free | Critical |
Config file permissions Checks if configuration files with credentials are readable by other server users | Paid | Warning |
Credentials in process list Passwords visible in the running process list. Any server user can read them. | Paid | Critical |
.git directory exposed via HTTP .git directory is publicly accessible. Anyone can download the source code and repository credentials. | Paid | Critical |
Firewall configured Checks which ports are open to the internet and if the firewall is active | Free | Critical |
IPv6 without firewall rules IPv6 enabled but no firewall rules. Ports blocked by IPv4 may be accessible via IPv6. | Paid | Critical |
Automatic attack blocking Checks if repeated failed login attempts are automatically blocked | Free | Critical |
Admin user accounts Checks how many accounts have full admin access. More than needed increases risk. | Paid | Warning |
System disk usage Disk occupancy level. A full disk can cause service outages and log loss. | Paid | Info |
SSL certificate expiry When a certificate expires, your site shows a security warning and users can't connect | Paid | Warning |
Apps running as admin Containers running as root. If the app is compromised, the attacker gains full server access. | Paid | Warning |
Docker bypasses firewall Docker can open ports to the internet that your firewall never sees | Paid | Critical |
Unprotected Docker API An unprotected Docker API gives anyone on the network full control over all your containers | Paid | Critical |
Docker socket mounted in container docker.sock mounted inside a container. If that container is compromised, the attacker controls all of Docker. | Paid | Critical |
Database open to internet Your PostgreSQL database is accessible from the internet. No credentials needed to connect. | Paid | Critical |
Cache database unprotected Redis without a password. Any process on your network can read or flush your session data | Paid | Critical |
MongoDB open to internet MongoDB accessible without authentication from the internet | Paid | Critical |
Login attack history How many failed login attempts in the last 24 hours and from which IPs | Paid | Info |
Top attacker IPs The addresses most actively trying to access your server, with reputation data | Paid | Info |
Active attack detected Unusually high number of login failures in the last hour, possible brute-force attack in progress | Paid | Warning |
What attackers see from outside Scan from our servers against your public IP. Shows what's truly accessible from the internet, regardless of your local firewall | Paid | Critical if open |